Software teams move quickly, and modern delivery cycles often require developers, testers, and stakeholders to exchange builds across offices, remote setups, and third-party environments. When those packages contain logs, sample databases, or configuration files, the risk of exposing sensitive information increases. Many teams reduce that risk by using a secure SFTP server that provides encrypted build transfers, controlled user access, and safer handling of test assets between departments.
Understand What Is Inside Every Build
A build package often contains more than application code. It may include test credentials, API keys, screenshots, customer-like records, and environment settings that reveal internal systems. If teams share these files casually, they may expose information that should remain private.
Before any transfer takes place, teams should review the contents of release packages and test bundles. A simple pre-share checklist can identify hidden files, debug notes, or outdated datasets that no longer need to travel with the build. This reduces both file size and security exposure.
Use Masked and Sanitized Test Data
One of the most common mistakes in software testing is using production data in lower environments. Real names, payment details, and contact records can appear in copied databases, creating unnecessary legal and reputational risk. Even internal sharing becomes dangerous when too many people gain access.
Instead, businesses should use masked or synthetic data for testing. Sanitized datasets preserve structure and realism while removing personal identifiers. This allows testers to validate workflows without exposing real customer information when builds are distributed across teams.
Choose Encrypted Transfer Methods
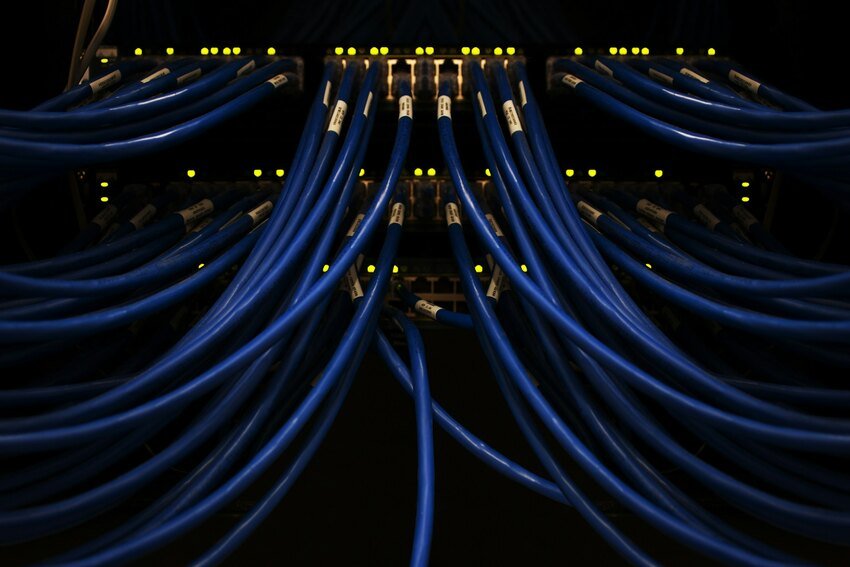
Email attachments and consumer-grade file sharing tools are convenient, but they are rarely the best option for sensitive testing materials. Files may be forwarded, stored in unmanaged locations, or accessed through weak permissions. That creates gaps in accountability.
Encrypted transfer platforms help protect files in transit and at rest. When teams send builds through secure channels with managed authentication, they reduce the chance of interception or accidental exposure. Strong transfer methods are especially important when external QA vendors or offshore teams are involved.
Control Access by Role and Need
Not everyone working on a project needs access to every build component. Developers may need source-related files, while testers only need executables, release notes, and approved datasets. Broad access creates unnecessary risk.
Role-based permissions help keep data exposure limited. Teams should grant access based on project responsibility, then remove permissions when work is complete. Temporary access controls are useful for contractors, short-term consultants, and client reviewers.
Maintain Version Discipline
When multiple teams test different builds at the same time, confusion can lead to risky behavior. Someone may resend an old package, upload an outdated database, or test against files that were never approved. This creates both quality and security problems.
Clear version naming standards help prevent mistakes. Each build should include a consistent identifier, release date, and environment label. Shared repositories should archive older versions separately so teams can locate what they need without mixing files.
Track Every Transfer Activity
Security improves when organizations know who accessed files, when transfers happened, and what was downloaded. Without logs, it becomes difficult to investigate incidents or prove compliance. Missing visibility can also slow internal audits.
Teams should use systems that provide detailed transfer records and user activity trails. These records help managers spot unusual behavior, repeated failed logins, or unauthorized downloads. They also support continuous improvement by showing where handoff delays occur.
Protect Remote and Cross-Functional Collaboration
Many testing teams now operate across multiple locations. Developers may be in one country, QA engineers in another, and business stakeholders elsewhere. That makes secure sharing even more important because data crosses networks and devices outside a single office perimeter.
Organizations should combine secure transfer tools with endpoint policies and staff awareness. Approved devices, strong passwords, and multi-factor authentication all strengthen protection. Security becomes more effective when process and technology work together.
Build Security Into the Release Workflow
Protecting test data should not be treated as a separate task added at the end of a sprint. It works best when security controls are built into normal release operations. Teams that automate packaging, scanning, permissions, and delivery reduce manual errors.
As software delivery speeds up, safe collaboration becomes a competitive advantage. Businesses that manage build sharing responsibly can move faster while protecting sensitive information, preserving trust, and keeping testing environments efficient for every team involved.