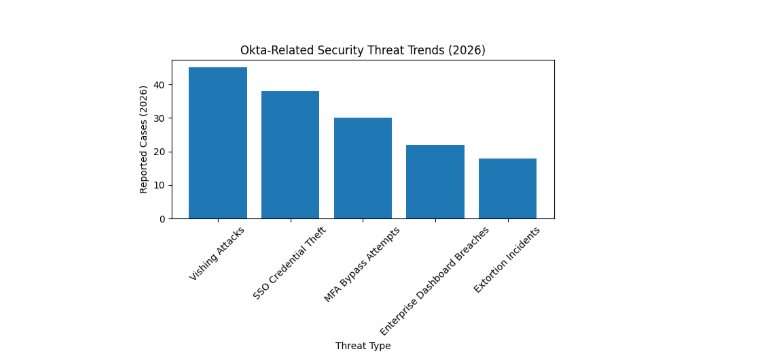
Cybersecurity news stories from 2026 focus on Okta because security experts investigate security breaches that occurred through advanced social engineering techniques. The latest developments show that threat actors now use enterprise authentication systems as their primary method for stealing login credentials and defeating multi-factor authentication systems.
Active Vishing Attacks Targeting Okta Users
Security researchers, along with Okta threat intelligence teams, have detected active voice phishing (vishing) campaigns that target Okta single sign-on (SSO) users. The attackers employ advanced phishing techniques through customized phishing-as-a-service kits to deceive employees into disclosing their login credentials along with their multi-factor authentication codes.
The method used by attackers differs from standard phishing because they establish direct phone contact with targets to gain their consent for authentication pushes. When attackers acquire login information, they can access all company SaaS systems, which enables them to conduct data theft and extortion activities.
ShinyHunters Claims Responsibility
The hacking group ShinyHunters has declared its involvement in multiple vishing campaigns that targeted Okta, Microsoft, and Google SSO systems. The group accessed enterprise dashboards based on intelligence reports, using them to extract confidential information needed for their extortion operation.
Okta has informed customers about the security threat, but security researchers have discovered ongoing investigations that will take time to verify which companies experienced the security breach.
Why This Matters: Identity Access Security at Risk
Worldwide businesses use Okta’s SSO technology to create a single authentication system, which enables them to access their cloud applications securely. The attackers have developed advanced social engineering techniques that now target identity providers rather than the systems these providers protect.
Threat actors use Okta’s software through its human vulnerabilities, which they exploit to collect user credentials for account access. The attackers can navigate through the system to internal dashboards while they gain higher privileges, which leads to multiple system accesses.
What Organizations Should Do?
To mitigate these evolving threats, businesses using Okta or similar SSO systems are advised to:
· Adopt phishing-resistant MFA methods like hardware keys or passkeys.
· Train employees on spotting sophisticated social engineering techniques.
· Monitor authentication logs for unusual access patterns.
· Isolate privileged accounts with enhanced controls.
Because threat actors now operate social engineering as a commercial service, organizations must implement defense measures that detect threats before they occur.



